
Hi, I'm Jesse Skinner.
I'm a self-employed web developer with over two decades of experience. I love learning new things, finding ways to improve, and sharing what I've learned with others.
I get the most joy from speeding up websites, reducing server costs, fixing difficult bugs, and modernizing legacy applications. I'd love to hear about your challenges and see how I can help!
Recent articles
Coding with ChatGPT April 23rd, 2023 I started using ChatGPT when it came out a few months ago. It was mind blowing to chat with a computer and have it...
What I learned from wearing a Continuous Glucose Monitor for two weeks April 2nd, 2023 A couple of weeks ago, I bought one of those Continuous Glucose Monitors (CGM). My nutritionist suggested I do this, even though I'm not...
Deploying a static site to Cloudflare Pages March 4th, 2023 I moved codingwithjesse.com to Cloudflare Pages this week! I was having some intermittent outages on my website in the hours before I wanted to...
Debugging a slow web app February 23rd, 2023 I got an email today from one of my clients, letting me know that one of his web apps was down. He said he...
Web apps that last February 19th, 2023 When you're building a new web application, or even a new feature, how can you ensure that you're not creating a nightmare code base...
Trying to decide what to do next? Follow the light. January 1st, 2023 Happy New Year! I've been trying to come up with a New Year's resolution, and it got me thinking about setting goals, finding and...
Recent videos
 6 ways GitHub Copilot helps you write better code faster
6 ways GitHub Copilot helps you write better code faster
 GitHub Copilot is super creepy
GitHub Copilot is super creepy
 Migrating my blog from Sapper to Svelte Kit
Migrating my blog from Sapper to Svelte Kit
 The Joy of Svelte is now available!
The Joy of Svelte is now available!
 Fixing a bug in Svelte, from issue to pull request
Fixing a bug in Svelte, from issue to pull request
 Switching from bash to fish shell
Switching from bash to fish shell
 7 Svelte features that bring me joy
7 Svelte features that bring me joy
 Introducing The Joy of Svelte
Introducing The Joy of Svelte
 Snowpack Quick Start
Snowpack Quick Start
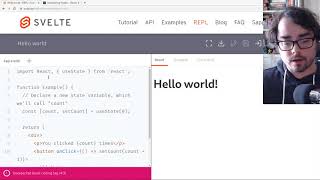 React Hooks vs Svelte
React Hooks vs Svelte
 Migrating my blog admin from React to Svelte and Sapper
Migrating my blog admin from React to Svelte and Sapper
 First time using Svelte, let's play Tic Tac Toe!
First time using Svelte, let's play Tic Tac Toe!
